Safeguarding the Pulse: Why Health tech Needs More Than Just a Firewall
Imagine a busy urban hospital in the heart of a digital-first city. In the Neonatal Intensive Care Unit (NICU), smart incubators are adjusting oxygen levels based on real-time data sent to a central dashboard. In the cardiology wing, a surgeon is performing a minimally invasive procedure, guided by high-definition, low-latency video feeds and AI-driven diagnostic overlays. This isn’t the future; it’s the present.
Now, imagine the screen flickers. The data feed lags. A subtle, malicious code has entered the network through an unpatched thermostat in the hospital’s climate control system, an entry point no one considered “medical.” Within minutes, the interconnectedness that made this hospital a marvel of modern medicine becomes its greatest vulnerability. The heartbeat of the facility, its data, stops.
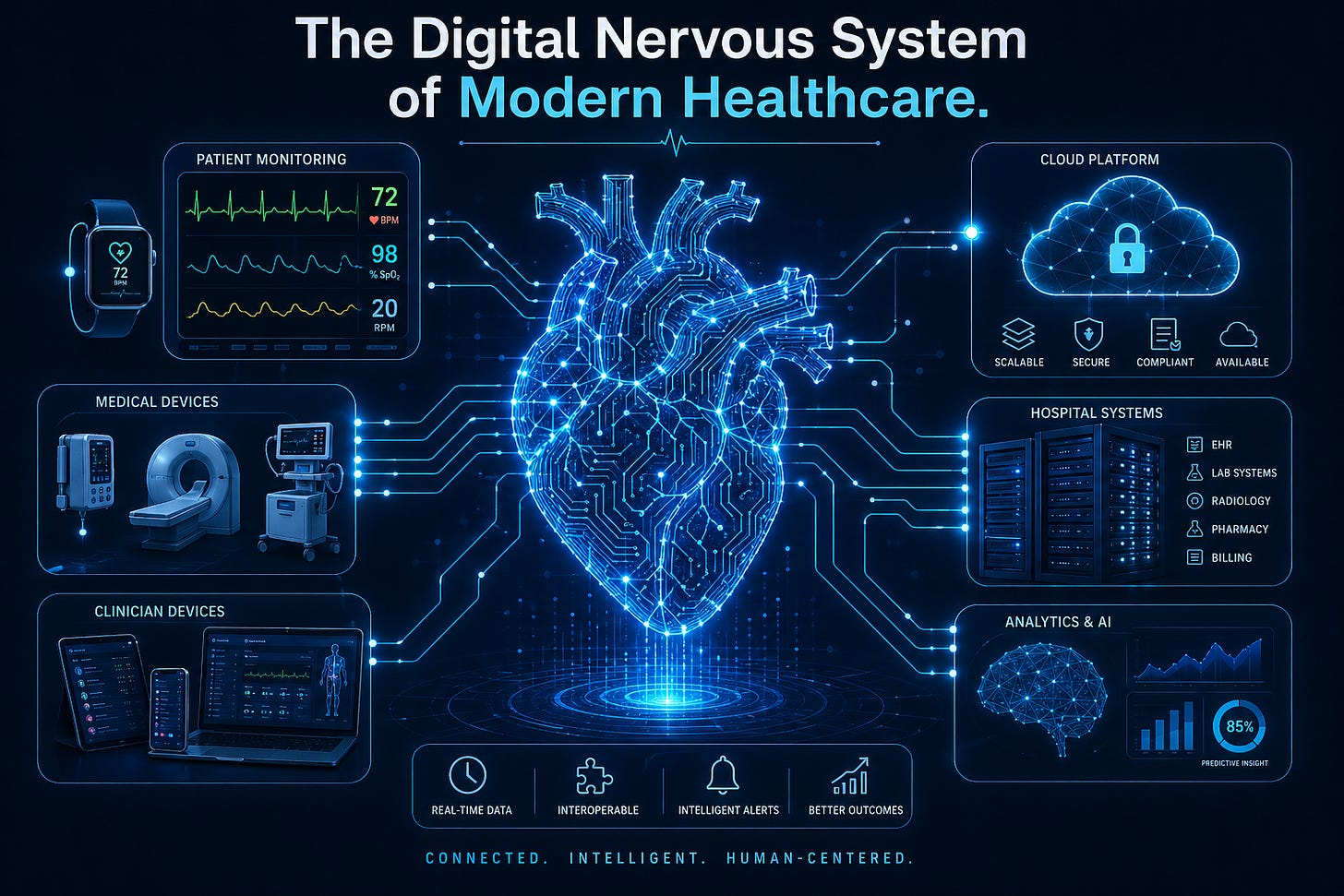
This is the reality Medlitics is built to prevent. We aren’t just building another healthtech platform; we are constructing the digital nervous system for the next generation of healthcare, one where the transition from strategy to execution is built on a foundation of “Zero-Failure” resilience.
The Imperative of Critical Infrastructure
In an increasingly interconnected world, the stability and functionality of modern societies hinge upon the uninterrupted operation of critical infrastructure. These vital assets, networks, and systems, from the energy grids that power our surgical theaters to the water treatment and communication networks that transmit patient vitals, are the bedrock of our daily lives. However, this very interconnectedness also presents an expanding attack surface, making critical infrastructure a prime target for sophisticated cyber threats.
From nation-state actors seeking to disrupt national capabilities to financially motivated cybercriminals, the risks are escalating, demanding a proactive and robust cybersecurity posture. The consequences of a successful cyberattack on health infrastructure can be catastrophic, leading to widespread service outages, economic turmoil, and even the loss of life. Fortifying these essential systems is not merely a technical challenge but a national security and economic imperative.
The Unique Challenge: Where IT Meets OT
A significant distinction in securing healthtech lies in the prevalence of Operational Technology (OT) and Industrial Control Systems (ICS), which manage physical processes. These systems often have long lifecycles, proprietary protocols, and real-time operational demands that make traditional IT security solutions unsuitable. The convergence of IT and OT environments further complicates the security landscape, creating new vectors for attack.
Effective security operations for critical infrastructure must address these unique characteristics. Key requirements include:
Continuous Monitoring: Implementing 24/7 surveillance of both IT and OT networks to detect anomalous behavior and potential threats in real-time.
Specialized Tools: Utilizing capabilities often requiring specialized tools capable of understanding ICS/SCADA protocols and behaviors.
Threat Intelligence: Identifying emerging threats and attack patterns relevant to critical infrastructure, leveraging threat intelligence feeds specific to OT/ICS environments.
Incident Response: Establishing well-defined and regularly tested incident response and recovery plans tailored to the unique operational constraints of critical infrastructure.
The NIST Cybersecurity Framework 2.0: Our Blueprint
Recognizing the need for a flexible, outcomes-based approach, the National Institute of Standards and Technology (NIST) developed the Cybersecurity Framework (CSF). With the release of CSF 2.0 in February 2024, the framework has been significantly enhanced to be even more relevant for critical infrastructure. It moves beyond a prescriptive checklist, focusing instead on desired cybersecurity outcomes.
1. GOVERN: The Strategic Pillar
The GOVERN function, a new addition, emphasizes integrating cybersecurity risk management decisions into an organization’s broader enterprise risk management strategy. It focuses on understanding and managing cybersecurity risk to the organizational mission and regulatory requirements.
2. IDENTIFY: Knowing the Landscape
IDENTIFY involves developing an organizational understanding to manage cybersecurity risk to systems, assets, data, and capabilities. In a medical environment, this encompasses asset management, risk assessment, and risk management strategy.
3. PROTECT: Safeguarding the Service
PROTECT focuses on implementing appropriate safeguards to ensure the delivery of critical infrastructure services. This covers identity management, access control, data security, and protective technology.
4. DETECT, RESPOND, & RECOVER: The Circle of Resilience
DETECT: Developing activities to identify the occurrence of a cybersecurity event, including continuous security monitoring.
RESPOND: Implementing activities to take action regarding a detected incident, covering response planning and mitigation.
RECOVER: Maintaining plans for resilience and restoring any capabilities or services impaired due to an incident.
Validation Through Data: The KPIs of Trust
To ensure that implemented controls are effective, organizations must establish clear validation mechanisms and measure performance using relevant Key Performance Indicators (KPIs). These provide objective evidence of security effectiveness and enable data-driven decision-making. Illustrative KPIs include:
GOVERN: Cybersecurity Risk Management Integration Rate (percentage of enterprise risk processes formally incorporating cybersecurity risk assessments).
IDENTIFY: Asset Inventory Coverage (percentage of critical IT/OT assets accurately documented and categorized).
PROTECT: Patching Compliance Rate (percentage of critical systems patched within defined service level objectives).
DETECT: Mean Time To Detect (MTTD) (average time taken to identify a cybersecurity incident from its occurrence).
RESPOND: Mean Time To Respond (MTTR) (average time taken to contain and eradicate a detected cybersecurity incident).
RECOVER: Recovery Time Objective (RTO) Attainment Rate (percentage of critical systems restored within their defined RTOs after an incident).
A Call to Action: Partnering for a Resilient Future
Securing the future of healthtech is a monumental and continuous undertaking that demands specialized expertise and a commitment to proactive, measurable security practices.
For Investors: We offer a framework-driven strategy that ensures the long-term viability and defensibility of healthtech assets.
For Healthcare Operators & Insurance: We provide the guidance and support to build and optimize security operations centers (SOCs), integrate advanced threat detection, and demonstrate a clear return on security investment through KPI monitoring.
For the Industry at Large: Our cybersecurity consulting firm stands ready to be your partner, bringing a wealth of experience in guiding critical infrastructure organizations through the complexities of risk management.
By taking these decisive steps and leveraging expert partnerships, we can build the robust defenses necessary to safeguard our shared future.
Join us at Medlitics. Let’s build a future where technology heals without fear.
Michael Fasere is the Founder and CEO of Medlitics and the founder and co-founder of Pashione and 1App Technologies. He has over two decades of experience in technology, cybersecurity, and startup building across Africa.